Sometimes, not all actions taken in the name of progress are for our good. I remember back in the days of Symbian OS, smartphones had Internet-on-demand instead of always-on Internet. That made it easy to know when your phone was making a connection in the background.
The way it worked was, our devices connected only when there was a need to – like when your email app made a connection to pull in fresh mail. If you launched the web browser to look up something, your phone made a connection. Otherwise, the Internet connection was in standby mode. And you could stop an app from making a connection.
Then came along always-on Internet. And as beautiful as it is, it came with security and privacy concerns. Your iPhone or Samsung Galaxy smartphone sends out data to servers owned by Apple and Google hundreds of times a day. An average of 340 times a day, to be precise. And this happens even when your phone is idle.
Other apps on your phone are also constantly shipping data off too. Most of that data includes details you stored on your phone and your location info. And all of this is possible because of always-on Internet. Modern smartphones are data mining machines.
A 2020 document published by the NSA says that, “Even if cellular service is turned off on a mobile device, Wi-Fi and BT can be used to determine a user’s location. Inconspicuous equipment (e.g., wireless sniffers) can determine signal strength and calculate location, even when the user is not actively using the wireless services. Even if all wireless radios are disabled, numerous sensors on the device provide sufficient data to calculate location.”
Do you get the picture? The onscreen toggles on your iPhone or Android smartphone do not 100% protect you. Apps bypass them every day. If you toggle off your location settings, your phone is still able to track you.
I have always maintained that the biggest factor in security and privacy is the human factor. You. Me. A huge chunk of security breaches happen because the human drops the ball. A weak password. Poor personal security habits (like leaving your phone lying around unprotected, or giving physical access to it in some other way).
Which is why I think that having physical kill switches on smartphones is a great idea.
What are physical Kill switches?
Hardware kill switches are physical buttons that can be used to disconnect a device. What might you need to disconnect? WiFi, Bluetooth, cellular signal, location, microphone, and camera. It should be within the power of the user to disconnect these with buttons. But why buttons when you can just put your phone in Airplane mode? Because it has been proven that even when in Airplane mode, devices collect data (including location data) and resume transmission right after you reconnect.
Why is a physical kill switch important?
A physical kill switch actually disables everything you need disabled. There is no bypassing them. When you use a hardware switch, those features cannot be remotely turned back on. You can deny access to your phone’s microphone with an app, yet a rogue app would still find a way around that. There is no bypass if you physically turn off of the microphone.
Lest I forget, we also used to be able to physically remove the battery of our phone. That is mostly a thing of the past now. Where all else failed to secure your phone, taking out the battery means that you can shut everything down properly – network radio, location tracking, Bluetooth, etc al. It is the ultimate physical kill switch.
As at right now, it is mostly feature phones that have retained this ability. We need that back in smartphones. We need smartphones whose batteries can be pulled out. I still have my Lumia 950, and the battery is removable.
There are not a lot of gadgets out there today that have any form of hardware kill switches. HP’s ENVY laptop has a camera kill switch. Instead of you putting tape over your camera lens, just shut it off with the switch. Nice.
Some smartphones with physical kill switches
There are a few smartphones that have hardware buttons to disconnect critical services on demand. Librem 5 is one of them. It has hardware buttons to turn off WiFi, Bluetooth, cellular signal, location, microphone, and the camera. These buttons physically disconnect these services, so there is no bypassing them by any rogue apps, or by Google, Apple, or even the NSA.
Librem 5 is pricey though. It comes in two variants – the regular Librem 5 for $1,199, and the made-in-America Librem 5 USA for $1,999.

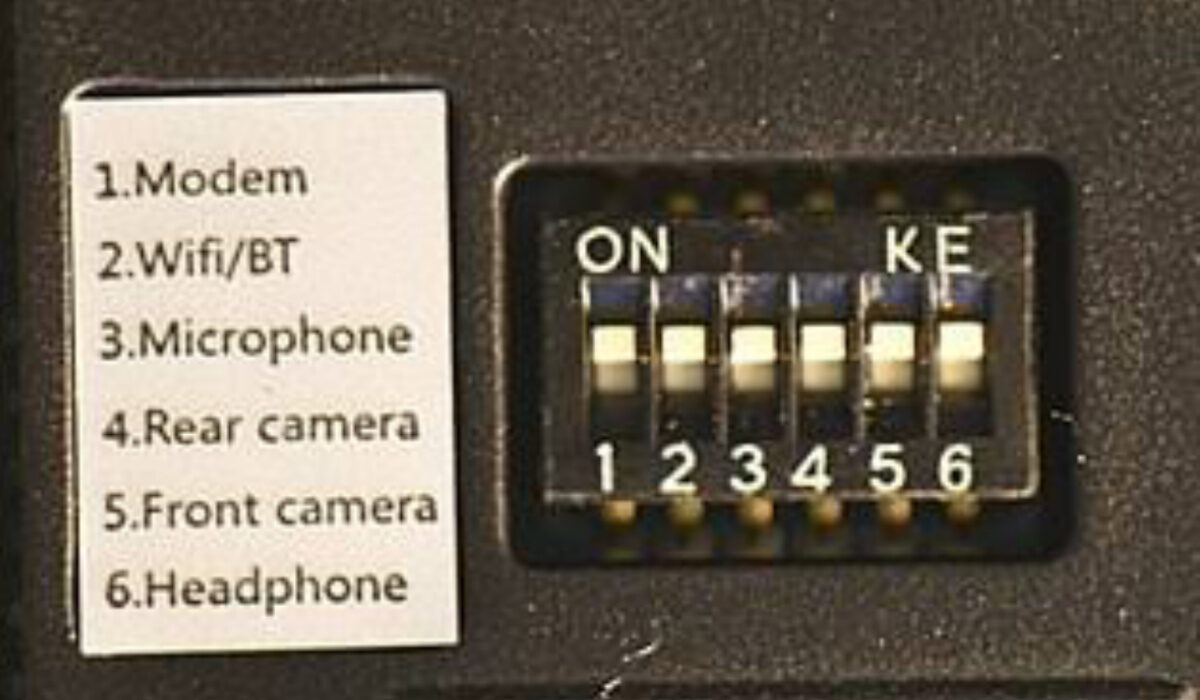
Another smartphone with physical kill switches is the PinePhone, and it takes it further than Librem 5. It has six buttons that control the modem, Wi-Fi, Bluetooth, microphone, rear camera, front camera, and the headphone jack. The PinePhone is available for a much more pocket-friendly price of $200.
Another cell phone with hardware kill switches is the Privacy Smartphone. It has physical kill switches to turn off your microphones, GPS, cellular modem, cameras, speakers, Bluetooth, and WiFi. The Privacy Smartphone costs €499 and is available on a monthly plan.
As far as privacy and security is concerned, phones with physical kill switches rank among the most secure, because when push comes to shove, no matter how secure an operating system is, having physical control to shut down the doorways, windows and backdoors to your device when you need it is the ultimate security.


2 thoughts on “Smartphones with physical kill switches”